How to overcome cybersecurity risk for remote work?
Working from home has grown considerably more common since the COVID-19 outbreak. Even after the epidemic has passed, experts believe remote working will continue to be popular in various industries....

Working from home has grown considerably more common since the COVID-19 outbreak. Even after the epidemic has passed, experts believe remote working will continue to be popular in various industries. Working from home is easy and offers many advantages, but it also exposes individuals and companies to cybersecurity dangers.
Table Of Content
According to a March 2022 research by Alliance Virtual Offices, which offers services to the remote workforce, remote work caused a 238% surge in cyber assaults during the COVID-19 pandemic. Additionally, in Gartner’s “7 top trends in cybersecurity for 2022,” the expansion of the attack surface caused by remote work and the increased usage of public cloud was identified as a critical cybersecurity concern.
That is why it is critical to take home cybersecurity seriously. In addition, most cybersecurity work-from-home vulnerabilities may be readily mitigated by adopting best practices.
How does remote work impact cybersecurity?
According to various security experts, a remote work environment might increase the danger of a data breach or other cyber assault for multiple reasons. First, remote work, particularly large-scale remote work, dramatically expands the possible attack areas that must be safeguarded.
Remote work broadened the possible attack surface and extended it beyond the usual perimeter defenses, such as firewalls and intrusion detection systems, that firms have historically erected to resist ransomware assaults, data breaches, and other sorts of cybercrime.
Furthermore, hackers are capitalizing on the transition to remote work settings by attacking flaws in the infrastructure that facilitates remote work and changing how they target the employees themselves.
Cybersecurity best practices for remote workers
- Implement basic security controls: Remote employees should utilize virtual private networks (VPN) to access company systems and adhere to a strict password policy that demands different passwords for various sites. Experts also suggested encrypting critical data and adopting cloud-based file sharing to keep data off worker computers.
- Create a robust vulnerability management program: Use a risk-based strategy to promptly resolve the most critical vulnerabilities and lower the number of unpatched vulnerabilities that hackers may exploit.
- Develop and implement a zero-trust framework: All users and devices should be needed to validate their access to the business environment.
- Ascertain that suitable cloud setups and access are in place: In public cloud infrastructures, misconfigurations are a primary source of security issues. Implement appropriate user access rules to minimize glitches, gaps, or errors that might expose the work environment to risk during cloud migration and operation.
- Create a continuous security awareness program: Educate users on potential new security dangers and the precautions that must be taken to keep the company secure.
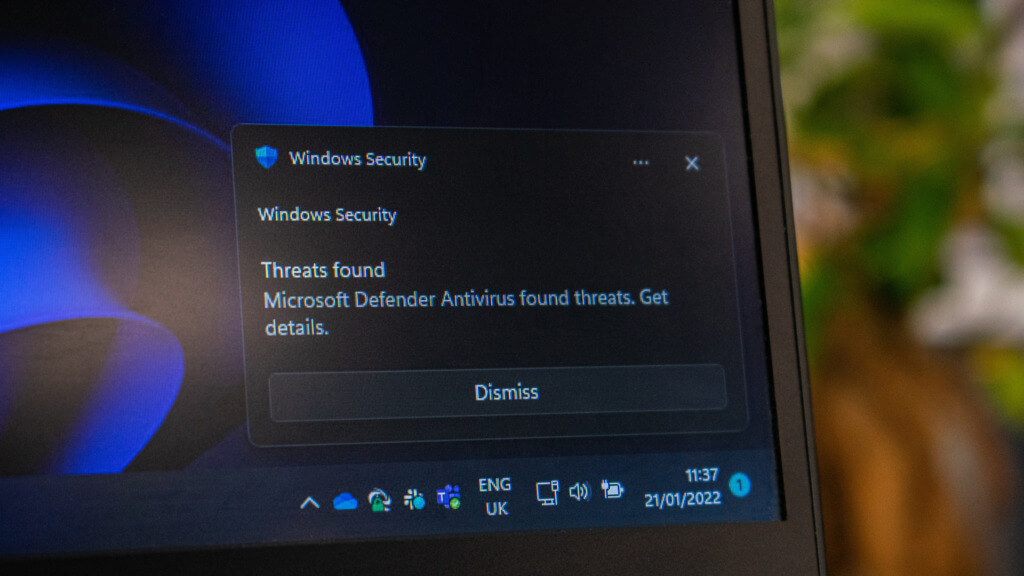
- Antivirus and internet security software should be used: Investing in a complete antivirus package for you and your staff is one of the most effective security advice for working from home. Antivirus suites do the hard work for you by providing automated remote work protection against various dangers.
- Use an all-in-one solution like Acronis Cyber Protect to safeguard your data: Acronis Cyber Protect is a next-generation solution that integrates backup, anti-malware, cybersecurity, and endpoint management functions such as vulnerability assessments, URL filtering, patch management, and more. It aims to protect the system from ransomware and allows users to back up and restore files or entire systems from a backup, ensuring business continuity.
Are your remote employees security-safe?
It is critical to take cybersecurity seriously when working remotely and in your company’s regular working environment. As the number of people working from home has grown worldwide, cybersecurity for remote workers has become a prominent concern. Individuals and organizations may minimize hazards and maintain safety by following cybersecurity remote work best practices.