Top cybersecurity vulnerabilities and how to mitigate them
In today’s digital world, cybersecurity vulnerabilities are a significant risk that can put individuals, businesses, and governments at risk of cyber-attacks. Cybersecurity vulnerabilities can...

In today’s digital world, cybersecurity vulnerabilities are a significant risk that can put individuals, businesses, and governments at risk of cyber-attacks. Cybersecurity vulnerabilities can range from weak passwords to phishing attacks and insider threats. This article will explore some of the most common cybersecurity vulnerabilities and how to mitigate them.
Table Of Content
- Phishing attacks: Don’t take the bait
- Weak passwords: Don’t let them unlock your data
- Unpatched systems: Don’t leave the door open
- Insider threats: Watch out for malicious employees
- Ransomware: Don’t let attackers hold your data hostage
- Malware: Protect your systems from infection
- Staying vigilant in the ever-evolving landscape of cybersecurity
Phishing attacks: Don’t take the bait
Phishing attacks are common cyber-attack involving tricking individuals into revealing their personal information. These attacks can occur via email, phone, or text message. Attackers often pose as a trusted entity, such as a bank or a government agency, to gain the victim’s trust. Once they have earned the victim’s trust, they will ask them to provide sensitive information, such as login credentials or credit card details.
To mitigate phishing attacks, educating employees on identifying suspicious emails and not clicking on any links or attachments that seem out of place is essential. One way to do this is through security awareness training. Employees must be taught to verify the sender’s identity before providing sensitive information. Additionally, implementing two-factor authentication can make it harder for attackers to gain access to sensitive data. Two-factor authentication requires users to give additional information, such as a code generated by a smartphone app, to log in.
Weak passwords: Don’t let them unlock your data
Weak passwords can make it easy for attackers to access a system or an account. Unfortunately, many people use the same simple password across multiple accounts, which puts them at risk of a cyber-attack.
To mitigate the risk of weak passwords, it is recommended to use complex passwords that include a combination of letters, numbers, and symbols. Passwords should be changed regularly and not be reused across multiple accounts. Additionally, implementing multi-factor authentication can provide an extra layer of security. Multi-factor authentication requires users to give additional information to log in, such as a code generated by a smartphone app or a fingerprint scan.
Unpatched systems: Don’t leave the door open
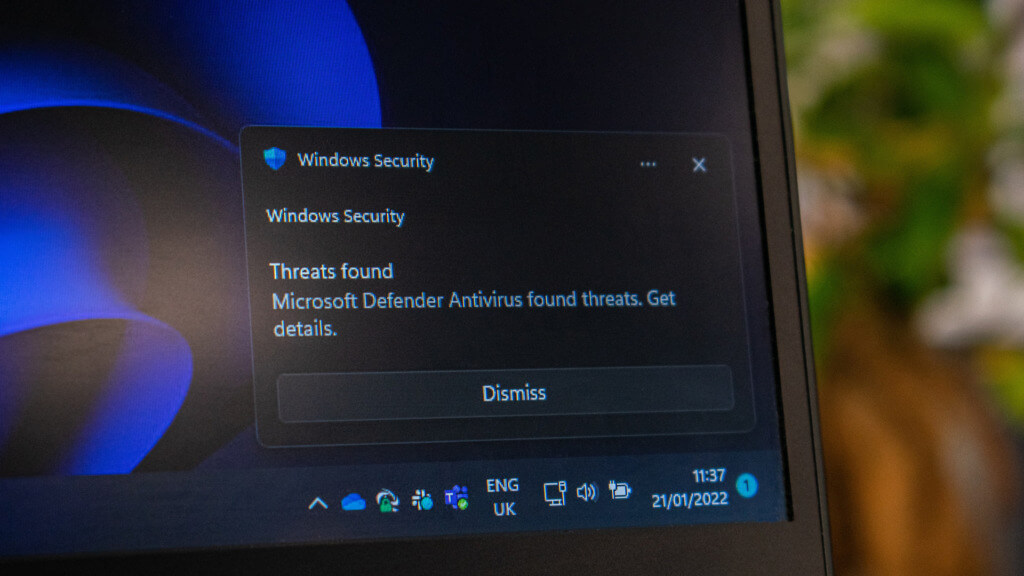
Software vulnerabilities are often discovered, and software companies release patches to fix these vulnerabilities. However, if a system is not updated, attackers can exploit these vulnerabilities. In addition, unpatched systems can also provide attackers with a way to gain network access.
To mitigate the risk of unpatched systems, keeping all software up to date with the latest security patches is essential. This includes operating systems, applications, and other software used within an organization. Regular software updates will ensure that known vulnerabilities are patched, making it harder for attackers to exploit them.
Insider threats: Watch out for malicious employees
An insider threat is a cybersecurity risk that comes from within an organization. It can be caused by employees, contractors, or partners with access to an organization’s systems, data, or facilities. Insider threats can be intentional or unintentional, and they can cause significant damage to an organization’s reputation, finances, and operations.
To mitigate the risk of insider threats, it is crucial to implement access controls limiting access to sensitive data and systems to those who need them to perform their job duties. Additionally, monitoring user activity and detecting abnormal behaviour can help detect potential insider threats before they can cause harm. This can be achieved through security information and event management (SIEM) systems, monitoring network traffic, detecting potential threats, and alerting security personnel.
Ransomware: Don’t let attackers hold your data hostage
Ransomware is malware that encrypts a victim’s data and demands a ransom payment in exchange for the decryption key. Attackers can deliver ransomware through phishing emails, malicious websites, or vulnerable software. Once ransomware infects a system, it can quickly spread to other systems, causing significant damage and downtime.
Implementing a robust backup and recovery plan to mitigate the risk of ransomware is important. This includes regularly backing up all critical data and storing the backups off-site. A backup copy of data can help organizations recover from a ransomware attack without paying the ransom. Additionally, implementing robust endpoint protection software can help detect and block ransomware before it can cause damage.
Malware: Protect your systems from infection
Malware is a term that describes a wide range of malicious software, including viruses, worms, Trojans, and ransomware. Malware can enter a system through various means, including phishing emails, malicious downloads, or vulnerability exploits. Once installed, malware can wreak havoc on systems, stealing sensitive information, causing system crashes, and allowing attackers to gain unauthorized access to a network.
To mitigate the risk of malware, it is essential to have comprehensive endpoint protection software, such as Acronis Cyber Protect. This all-in-one cybersecurity solution includes powerful anti-malware protection, backup and recovery, vulnerability assessment, patch management, and remote desktop management capabilities. With Acronis Cyber Protect, organizations can proactively detect and block malware before it can cause damage and quickly recover from a malware attack.
In addition to endpoint protection, it is essential to follow best practices for avoiding malware infections. This includes being cautious when downloading files or clicking on links, keeping software up to date, and implementing strong passwords and multi-factor authentication. Regular employee training on safe computing practices can also help mitigate the risk of malware infections.
Staying vigilant in the ever-evolving landscape of cybersecurity
Cybersecurity vulnerabilities are a significant risk to organizations, but there are ways to mitigate these risks. By implementing best practices such as educating employees, implementing strong passwords and access controls, and keeping systems up to date, organizations can significantly reduce their risk of a cyber-attack. It is also essential to be vigilant and proactive in identifying and addressing potential vulnerabilities before attackers can exploit them. Organizations can protect their systems and data from cyber-attacks by taking these steps. It’s important to remember that cybersecurity is an ongoing process and requires constant monitoring and updating to stay ahead of potential threats.














